Showing
- docs.it4i/get-started-with-it4innovations/accessing-the-clusters/graphical-user-interface/graphical-user-interface.md 15 additions, 0 deletions...ters/graphical-user-interface/graphical-user-interface.md
- docs.it4i/get-started-with-it4innovations/accessing-the-clusters/graphical-user-interface/vnc.md 217 additions, 0 deletions...ns/accessing-the-clusters/graphical-user-interface/vnc.md
- docs.it4i/get-started-with-it4innovations/accessing-the-clusters/graphical-user-interface/x-window-system.md 132 additions, 0 deletions...-the-clusters/graphical-user-interface/x-window-system.md
- docs.it4i/get-started-with-it4innovations/accessing-the-clusters/introduction.md 16 additions, 0 deletions...ith-it4innovations/accessing-the-clusters/introduction.md
- docs.it4i/get-started-with-it4innovations/accessing-the-clusters/shell-access-and-data-transfer/pageant.md 12 additions, 0 deletions...ng-the-clusters/shell-access-and-data-transfer/pageant.md
- docs.it4i/get-started-with-it4innovations/accessing-the-clusters/shell-access-and-data-transfer/putty.md 59 additions, 0 deletions...sing-the-clusters/shell-access-and-data-transfer/putty.md
- docs.it4i/get-started-with-it4innovations/accessing-the-clusters/shell-access-and-data-transfer/puttygen.md 51 additions, 0 deletions...g-the-clusters/shell-access-and-data-transfer/puttygen.md
- docs.it4i/get-started-with-it4innovations/accessing-the-clusters/shell-access-and-data-transfer/ssh-keys.md 112 additions, 0 deletions...g-the-clusters/shell-access-and-data-transfer/ssh-keys.md
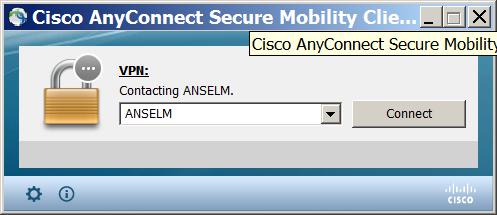
- docs.it4i/get-started-with-it4innovations/accessing-the-clusters/shell-access-and-data-transfer/vpn-connection-fail-in-win-8.1.md 19 additions, 0 deletions...ccess-and-data-transfer/vpn-connection-fail-in-win-8.1.md
- docs.it4i/get-started-with-it4innovations/applying-for-resources.md 12 additions, 0 deletions...get-started-with-it4innovations/applying-for-resources.md
- docs.it4i/get-started-with-it4innovations/obtaining-login-credentials/certificates-faq.md 161 additions, 0 deletions...novations/obtaining-login-credentials/certificates-faq.md
- docs.it4i/get-started-with-it4innovations/obtaining-login-credentials/obtaining-login-credentials.md 164 additions, 0 deletions...btaining-login-credentials/obtaining-login-credentials.md
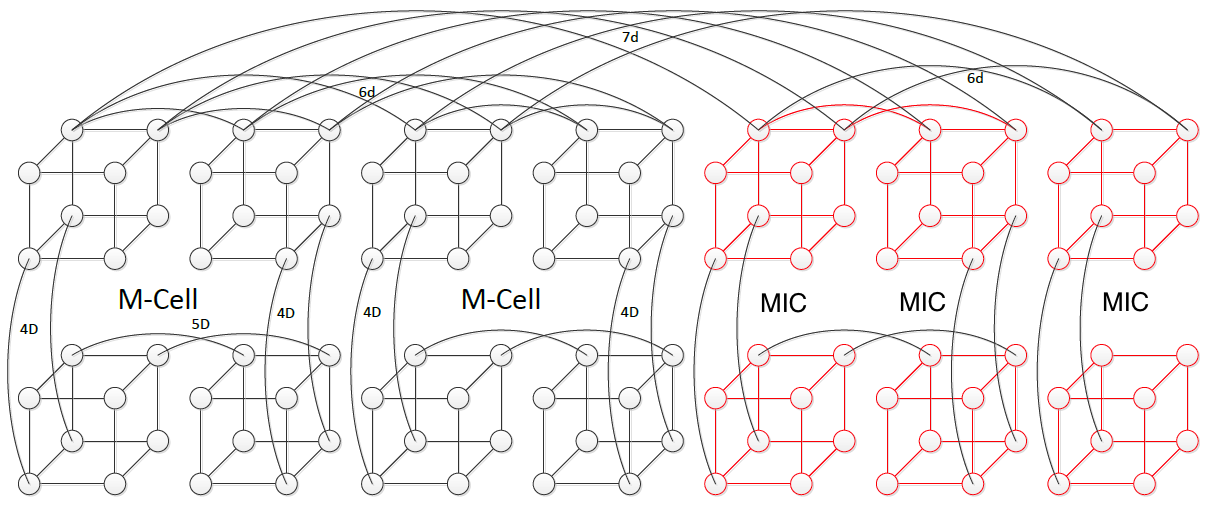
- docs.it4i/img/7D_Enhanced_hypercube.png 0 additions, 0 deletionsdocs.it4i/img/7D_Enhanced_hypercube.png
- docs.it4i/img/AMsetPar1.png 0 additions, 0 deletionsdocs.it4i/img/AMsetPar1.png
- docs.it4i/img/Anselmprofile.jpg 0 additions, 0 deletionsdocs.it4i/img/Anselmprofile.jpg
- docs.it4i/img/Authorization_chain.png 0 additions, 0 deletionsdocs.it4i/img/Authorization_chain.png
- docs.it4i/img/Fluent_Licence_1.jpg 0 additions, 0 deletionsdocs.it4i/img/Fluent_Licence_1.jpg
- docs.it4i/img/Fluent_Licence_2.jpg 0 additions, 0 deletionsdocs.it4i/img/Fluent_Licence_2.jpg
- docs.it4i/img/Fluent_Licence_3.jpg 0 additions, 0 deletionsdocs.it4i/img/Fluent_Licence_3.jpg
- docs.it4i/img/Fluent_Licence_4.jpg 0 additions, 0 deletionsdocs.it4i/img/Fluent_Licence_4.jpg
docs.it4i/img/7D_Enhanced_hypercube.png
0 → 100644
154 KiB
docs.it4i/img/AMsetPar1.png
0 → 100644
46.5 KiB
docs.it4i/img/Anselmprofile.jpg
0 → 100644
19.6 KiB
docs.it4i/img/Authorization_chain.png
0 → 100644
26.8 KiB
docs.it4i/img/Fluent_Licence_1.jpg
0 → 100644
78.9 KiB
docs.it4i/img/Fluent_Licence_2.jpg
0 → 100644
81.4 KiB
docs.it4i/img/Fluent_Licence_3.jpg
0 → 100644
87 KiB
docs.it4i/img/Fluent_Licence_4.jpg
0 → 100644
80.5 KiB